Tel Aviv, Israel, October 29th, 2025, CyberNewsWire
Sweet Security Brings Runtime-CNAPP Power to Windows
Sweet Security, a leader in Runtime Cloud and AI security solutions, today announced an extension of its Runtime CNAPP sensor to include Windows environments. With this launch, organizations can secure Windows workloads and applications in the cloud. The new capability brings the same deep visibility, real-time detection, risk prioritization, and automated investigation that power Sweet’s Runtime CNAPP for Linux to one of the most complex and widely used operating systems in the enterprise cloud.
Protecting cloud workloads running on the Windows operating system has long been a challenge due to the complexity and the wide range of attack vectors that adversaries can exploit. Many existing solutions rely on an EDR agent that’s been repurposed for the cloud, but was ultimately designed for totally different attack scenarios than the ones present in the cloud.
Sweet’s Windows sensor was developed specifically for the cloud using Rust, which allows for minimal resource footprint. Sweet’s Windows sensor covers all the usual attack vectors, such as DLL injection, registry manipulation, PowerShell scripting, etc., in addition to covering application-level requests and responses (Layer 7 data), peering into applications’ behavior.
Like all of Sweet’s runtime signals, the Windows sensor relies on Sweet’s renowned behavioral baselining technology, which allows it to detect not just known attack techniques or binary signatures, but also the abuse of legitimate tools for malicious purposes. The signals are also cross-correlated with cloud audit logs and cloud identities (CDR and ITDR) for maximum context and observability.
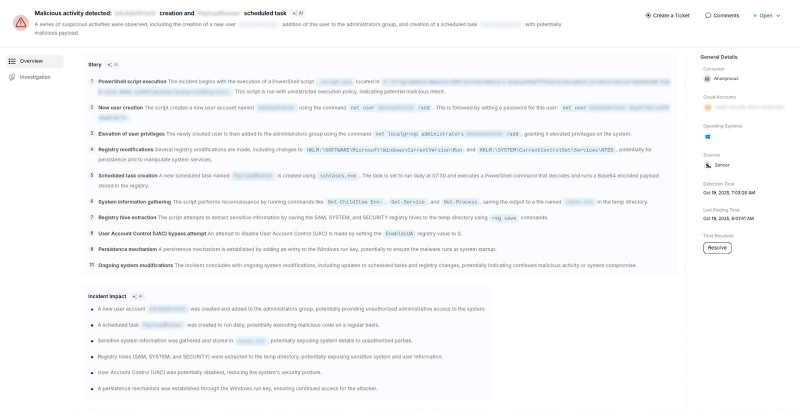
In a recent customer evaluation, Sweet’s Windows sensor identified a credential-dumping attempt within seconds. The sensor correlated PowerShell execution, registry export, and file creation anomalies that traditional sensors failed to detect. From detection to full investigation, the entire process took under two minutes, demonstrating how Sweet’s behavioral and AI-powered detection capabilities accelerate response times and reduce investigation noise.
 With Sweet’s Windows runtime sensor, customers now have a clear view of activity across all workloads. They are now able to detect and address potential threats faster and with greater confidence, protecting critical workloads and maintaining business continuity.
With Sweet’s Windows runtime sensor, customers now have a clear view of activity across all workloads. They are now able to detect and address potential threats faster and with greater confidence, protecting critical workloads and maintaining business continuity.
With the extension to Windows, Sweet Security now leverages its patented LLM-powered correlation and investigation, behavioral baseline, and L7 capabilities to provide full-stack protection for the cloud with its runtime CNAPP, including:
- Cloud Application Detection and Response (CADR)
- Cloud Security Posture Management (CSPM)
- Kubernetes Security Posture Management (KSPM)
- Cloud Infrastructure Entitlements Management (CIEM)
- Compliance & Governance
- Vulnerability Management
- CI/CD Pipeline Hardening
- Identities Security (ITDR)
- API Security
- Dynamic Application Security Testing (DAST)
- Data Security (DSPM)
“This launch marks a major step forward for the entire cloud security industry,” said Orel Ben Ishay, co-founder and VP of R&D, Sweet Security. “Windows has historically been a blind spot for runtime protection. By bringing the same depth of behavioral insight, AI-powered detection, and real-time investigation that we deliver for Linux to Windows environments, we are eliminating one of the most significant visibility gaps in cloud security. Detection and full investigation can now take less than two minutes, providing teams with actionable insights faster than ever. This is a foundational step toward our vision of universal runtime protection across all cloud workloads.”
With this launch, Sweet Security continues to redefine runtime-native CNAPP, helping organizations detect and stop sophisticated attacks before they impact critical cloud workloads.
For more information on Sweet’s Windows sensor or Runtime CNAPP, users can book a demo today or contact their customer support representative.
About Sweet Security
Sweet Security is redefining enterprise cloud protection. As the leading provider of Runtime CNAPP solutions and a pioneer in AI Security, Sweet unifies runtime context with advanced AI intelligence to protect the modern enterprise across applications, workloads, and infrastructure. Its platform delivers real-time detection and response, vulnerability and posture management, identity threat protection, and API security—powered by patent-pending, LLM-driven detection, reducing alert noise to just 0.04%. By bridging cloud and AI security, Sweet enables organizations to accelerate innovation, reduce operational risk, and achieve industry-leading MTTR times.
Privately funded, Sweet is backed by Evolution Equity Partners, Munich Re Ventures, Glilot Capital Partners, CyberArk Ventures, and an elite group of angel investors. For more information, users can visit sweet.security.
Contact
Chloe Amante
Montner Tech PR
[email protected]
Leave a Reply