Dubai, United Arab Emirates, November 20th, 2024, CyberNewsWire
ANY.RUN announced the launch of Smart Content Analysis, an advanced mechanism within its Automated Interactivity feature that enables the service to automatically detonate complex malware and phishing attacks, helping users speed up their investigations and gain in-depth insights into malicious behavior.
About Smart Content Analysis
Smart Content Analysis is a mechanism that allows the ANY.RUN sandbox to execute multi-stage cyber attacks without any user involvement. It does this by following three main steps:
- Scanning uploaded files to locate critical components, such as URLs and email attachments.
- Identifying the key components detonation of which moves the attack forward, including URLs embedded within QR codes or rewritten by security filters.
- Engaging with the malicious content in a controlled environment, for instance, by opening URLs in a browser or running payloads found in email archive attachments to observe their behavior.
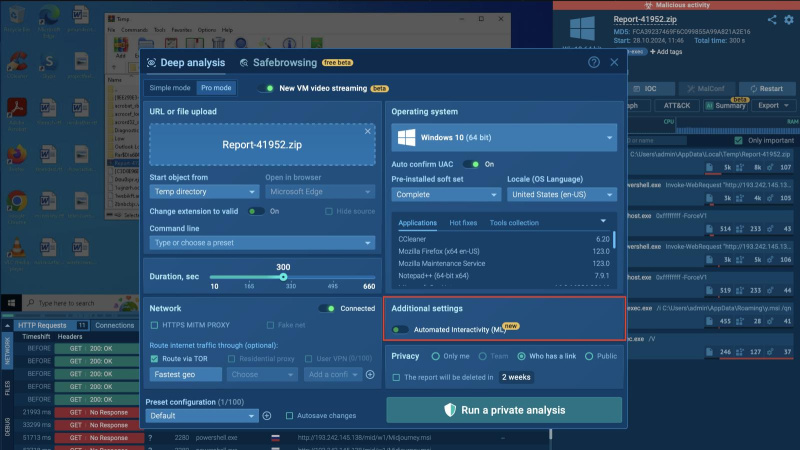 Automated Interactivity toggle inside ANY.RUN sandbox
Automated Interactivity toggle inside ANY.RUN sandbox
Detonating a Multi-Stage Attack with Automated Interactivity
With this new upgrade, ANY.RUN’s sandbox can automatically execute the following types of content found at different stages of complex cyber attacks:
- URLs inside QR codes
- Modified links
- Multi-stage redirects
- Email attachments
- Payloads with archives
Consider the following multi-stage phishing attack analyzed with Automated Interactivity.
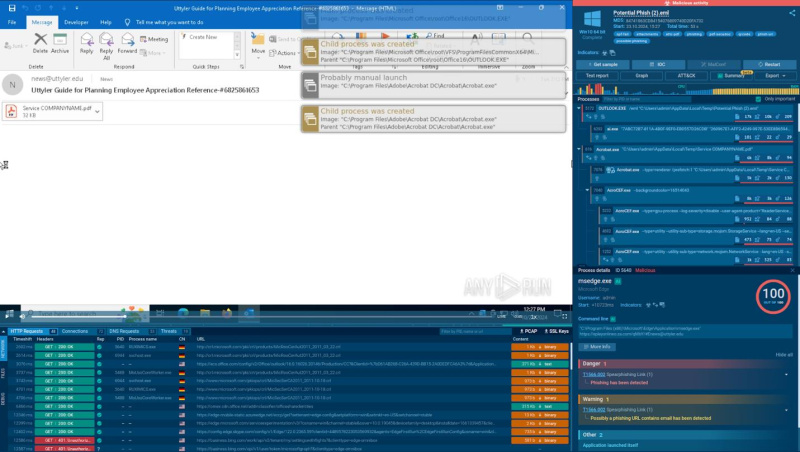 The phishing email analyzed with Automated Interactivity
The phishing email analyzed with Automated Interactivity
The system automatically opens the .eml file submitted by the user via Outlook, detects a PDF attachment, and scans its contents.
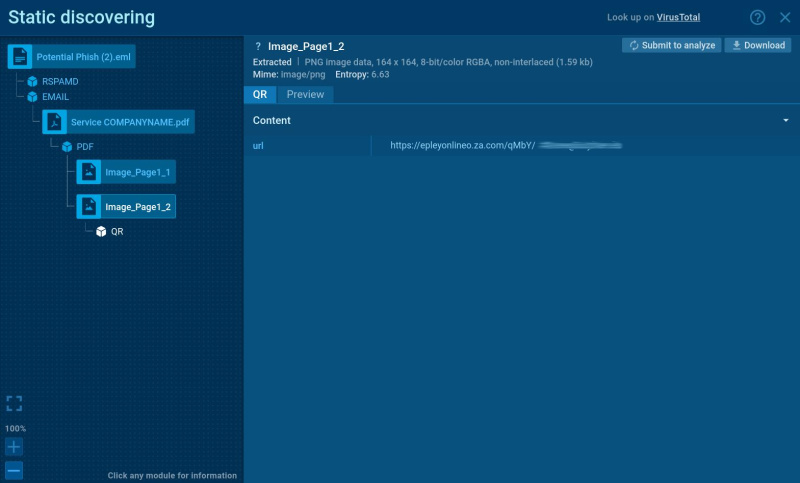 The static analysis module in ANY.RUN sandbox reveals the link hidden in the QR
The static analysis module in ANY.RUN sandbox reveals the link hidden in the QR
Inside the PDF, it identifies a QR code, instantly extracts the embedded URL, and opens it in a browser.
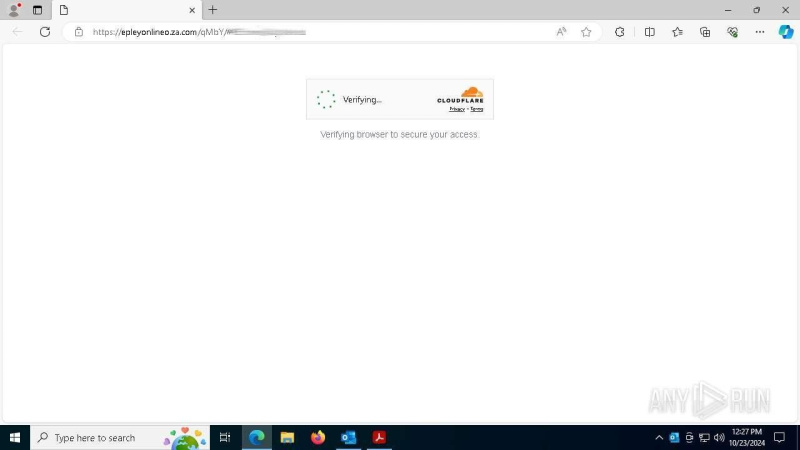 ANY.RUN sandbox automatically solving CAPTCHA challenges
ANY.RUN sandbox automatically solving CAPTCHA challenges
When faced with a CAPTCHA challenge, commonly used to evade detection, the feature successfully solves it and moves on to the next stage of the attack.
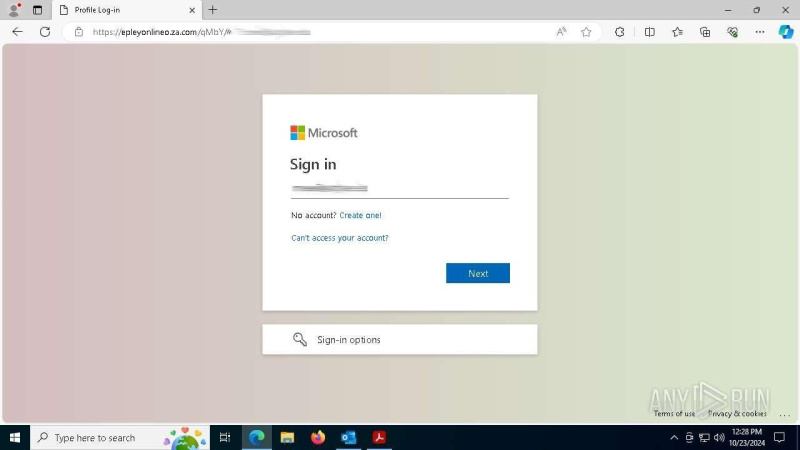 The final phishing page designed to steal victims’ credentials
The final phishing page designed to steal victims’ credentials
Eventually, it successfully reaches the final phishing page, not only ensuring complete detection of the attack, but also providing additional context on the threat at hand.
Adaptive to New Threats
ANY.RUN’s Smart Content Analysis is built to adapt to the changing threat landscape. With regular attack scenario updates from the ANY.RUN threat research team, the system remains aligned with emerging attack methods, allowing it to handle even the latest and most evasive threats.
Exploring Smart Content Analysis
Automated Interactivity helps security professionals streamline and improve their threat investigations:
- Less manual effort: No more wasted clicks. Let the sandbox handle repetitive actions so you can focus on the bigger picture.
- Faster, deeper insights: Go beyond surface detections with simulations that bring hidden threat layers to light.
- Speedy analysis: Accelerate your analysis with automation that moves as fast as you do, from simple phishing links to layered attack chains.
Users can request a 14-day free trial of ANY.RUN’s Interactive Sandbox to try Automated Interactivity for free.
𝐀𝐛𝐨𝐮𝐭 𝐀𝐍𝐘.𝐑𝐔𝐍
ANY.RUN serves over 500,000 cybersecurity professionals globally, offering an interactive platform for malware analysis targeting Windows and Linux environments. With advanced threat intelligence tools such as TI Lookup, YARA Search, and Feeds, ANY.RUN enhances incident response and provides analysts with essential data to counter cyber threats effectively.
Users can connect through social media: X, LinkedIn
Contact
ANYRUN FZCO
[email protected]
+1 657-366-5050
Leave a Reply